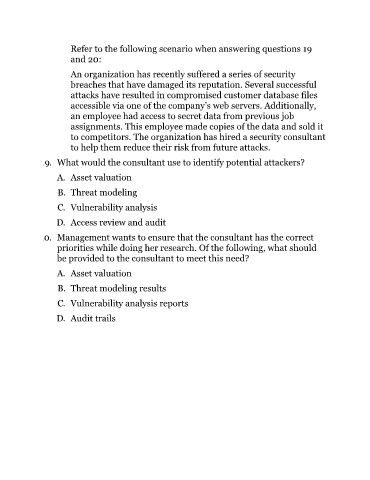
Page 1070 - (ISC)² CISSP Certified Information Systems Security Professional Official Study Guide
P. 1070
Refer to the following scenario when answering questions 19
and 20:
An organization has recently suffered a series of security
breaches that have damaged its reputation. Several successful
attacks have resulted in compromised customer database files
accessible via one of the company’s web servers. Additionally,
an employee had access to secret data from previous job
assignments. This employee made copies of the data and sold it
to competitors. The organization has hired a security consultant
to help them reduce their risk from future attacks.
19. What would the consultant use to identify potential attackers?
A. Asset valuation
B. Threat modeling
C. Vulnerability analysis
D. Access review and audit
20. Management wants to ensure that the consultant has the correct
priorities while doing her research. Of the following, what should
be provided to the consultant to meet this need?
A. Asset valuation
B. Threat modeling results
C. Vulnerability analysis reports
D. Audit trails